A rather older news item that triggered my interest, especially since I saw Eagle Eye last night – a Hollywood movie that deals with a super surveillance computer gone wild in a “2001: A Space Odyssey“-sense:
Mobiles are assigned a temporary anonymous number by the network called a temporary mobile subscriber identity, or TMSI, which the phone periodically transmits to advise of its location.
As the phone moves through the different regions served by different base stations, that number changes.
Path Intelligence’s approach, called FootPath, directly detects that TMSI transmission from phones. No access to the mobile networks themselves is necessary, so the information that they glean is specific to a user, but completely anonymous.
The TMSIs can only be associated with a number by the mobile operators and Path Intelligence encrypt the TMSIs that they acquire as an added level of security.
…
It has been approached by humanitarian workers in refugee camps, where a lack of central planning means it is often difficult to site services such as clinics where they can be best used.
The system will also be useful for researching the layout of, for example, train stations. (source)
“Reality mining” (Hujambo Nathan :-) – as interesting as it is (I for one would like to use such a system to see where ppl gather in cities to find the ideal location for a public toilet) – tells me that there’s still much more to mobile phone networks than what you may assume it already is. Contrary to the average communication or data connection needs, they also work as passive tracking devices and are constantly carried around by consumers. Meaning?
Mobile phones are as close as companies will ever get to a customer (unless they find a way of smuggling subliminal messages or ads in our dreams – as seen on Futuruma).
If you still believe that the mobile communication sector is just a temporary hype, this should open your eyes for the future. Don’t be fooled by current limited technologies (e.g. crippled mobile browsers) – the technology is going to evolve to a much bigger network of services that provide comfort to its users and valuable user data to some few operators who control the data.
Germany’s T-Mobile recently had a very embarrassing scandal where user data of 17 million (!) customers got “lost” a year ago, including those private numbers of celebrities & other VIPs. And this although there are already very strict data privacy laws in Germany that would normally prevent such a faux-pas.
So, obviously, it’s not only those big players like T-Mobile or Vodafone who provide the necessary mobile communication networks, but instead the few companies that collect all that gathered user data and use it for their own services. Is this good or bad?
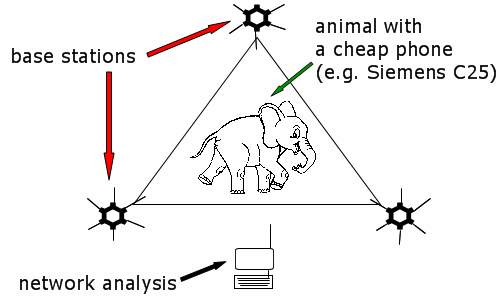
Coming back to the initial story: the triangulation method with it’s unique user IDs also reminds me of another AfriGadget-hack that’s prolly already out there – but if not, here’s my 2cent-idea: cheap mobile phones with stripped displays and small solar panels attached to the back cover that are then used as (cheaper) mobile tracking devices in nature preserves. Contrary to the old-fashioned Tx units, tracking equipment could be decentralized as it would rely on the base stations of the network (that, fortunately, often also cover nature parks) and consequently use less energy for a signal.
I sometimes wonder why I went into the water & sanitation business instead of focussing on my old interest from back in the days… :-)
p.s.: “we are based in the UK and the penetration of cell phones here is 108%, so we pretty much get everybody.” (source)

sijambo!